Le Juste Web is specialized in Classic ASP websites maintenance on the IIS platform. We regularly allow our customers to reach huge performance gains.
With 15 to 25% of the web server market shares (number varies according to studies), Microsoft Internet Information Services (IIS) is one of the most used web servers in the world, behind Apache and NGinx. Microsoft IIS 7/8/10 is the web server required to run Classic ASP applications, but it suffers from a bad reputation due to performance, session, or cache issues. Still, a well-configured IIS server is really a "race beast". As of today, more than 1,000,000 public websites still rely on the Classic ASP platform. The number of intranets, extranets and enterprise systems is estimated to be about 5 times greater (5,000,000).
In fact, the default Microsoft IIS configuration is too generic, and is not optimized to maximize the potential of Classic ASP scripts, whether the scripting language used is VBScript or JScript. This configuration have to be modified. Now developing for 24 years on the IIS platform with the Classic ASP infrastructure, and over the course of our company history, we have become experts in the Art of configuring the hundreds of parameters that IIS propose (and sometimes hide), and provide you with excellent (and stunning) performance gains for your Classic ASP application. We work on your dedicated, in-house / on-premise, virtualized or VPS servers. Many optimizations are even possible if you host your system on shared hosting.



How to drastically improve IIS performance for Classic ASP

There is no need to migrate your Classic ASP application to another platform (PHP, Apache, ASP.NET). In 9 out of 10 cases, it is faster and less expensive to keep your existing application by optimizing the configuration of the ASP IIS web server responsible for running it. As we have a very sharp focus on Classic ASP, this qualifies us to refactor and rewrite all or part of your ASP code base to make it much faster, and thus ensure its stability, while a complete migration to a new infrastructure would take months and require many financial resources.
We regularly optimize the IIS 7/8/10 web servers configuration on behalf of many customers, and help them deal with the performance issues they were experiencing so that they are a thing of the past. This way, our clients can peacefully retain and maintain their Classic ASP applications in a functional state, including in scalability scenarios. Contact our technical sales to express your project.
Improve speed and stability
Our IIS 7/8/10 web server configuration audit service consists of investigating your server infrastructure as well as all the used components that contribute to the exploitation of your ASP 3 based website. This process is aimed at identifying, reducing and / or eliminating the symptoms you have told us. The main goal is to bring you significant gains in speed, stability, as well as the load capacity of your application. Our service implements all human, technical, computer and documentary resources to achieve this objective.
Our IIS 7/8/10 configuration audit service
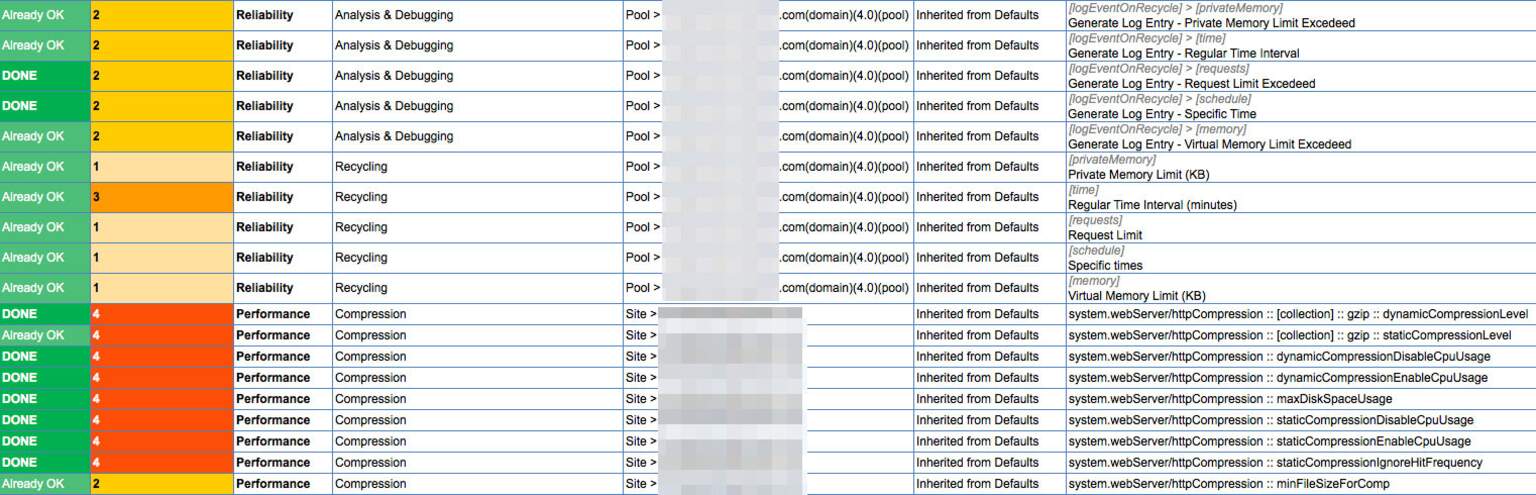
In order to bring dramatic performance gains to IIS 7/8/10, we are first conducting an IIS inspection phase. This audit consists of a detailed analysis of your IIS server configuration settings, accessible from the IIS "Configuration Editor ". We are also looking at some advanced settings that are only accessible from the "applicationHost.config" file, to diagnose the causes of the malfunctions you told us initially.
At the end of our audit, we provide you with a detailed and accurate report of the examined parameters, their status, and we then formulate a prioritized action plan containing accurate recommendations of which parameters need to be modified, accompanied by the new values that we recommend you to settle. Outsource this tedious task to our team.
Each of our recommendations is clearly documented and substantiated and based on the needs of your specific case, because each ASP application is different. Lost sessions or memory overflow issues will not require the same settings as scalability issues that could lead to HTTP 503 errors, often due to request queue size or slow database accesses.



When is an IIS configuration audit needed?
Our IIS / Classic ASP server configuration audit and tuning service will be a great help to you in many cases , such as:
- You are experiencing premature loss of sessions
- Accessing your Classic ASP websites / applications is slow
- Accessing your Classic ASP websites / applications does not support scalability when too many visits occurs
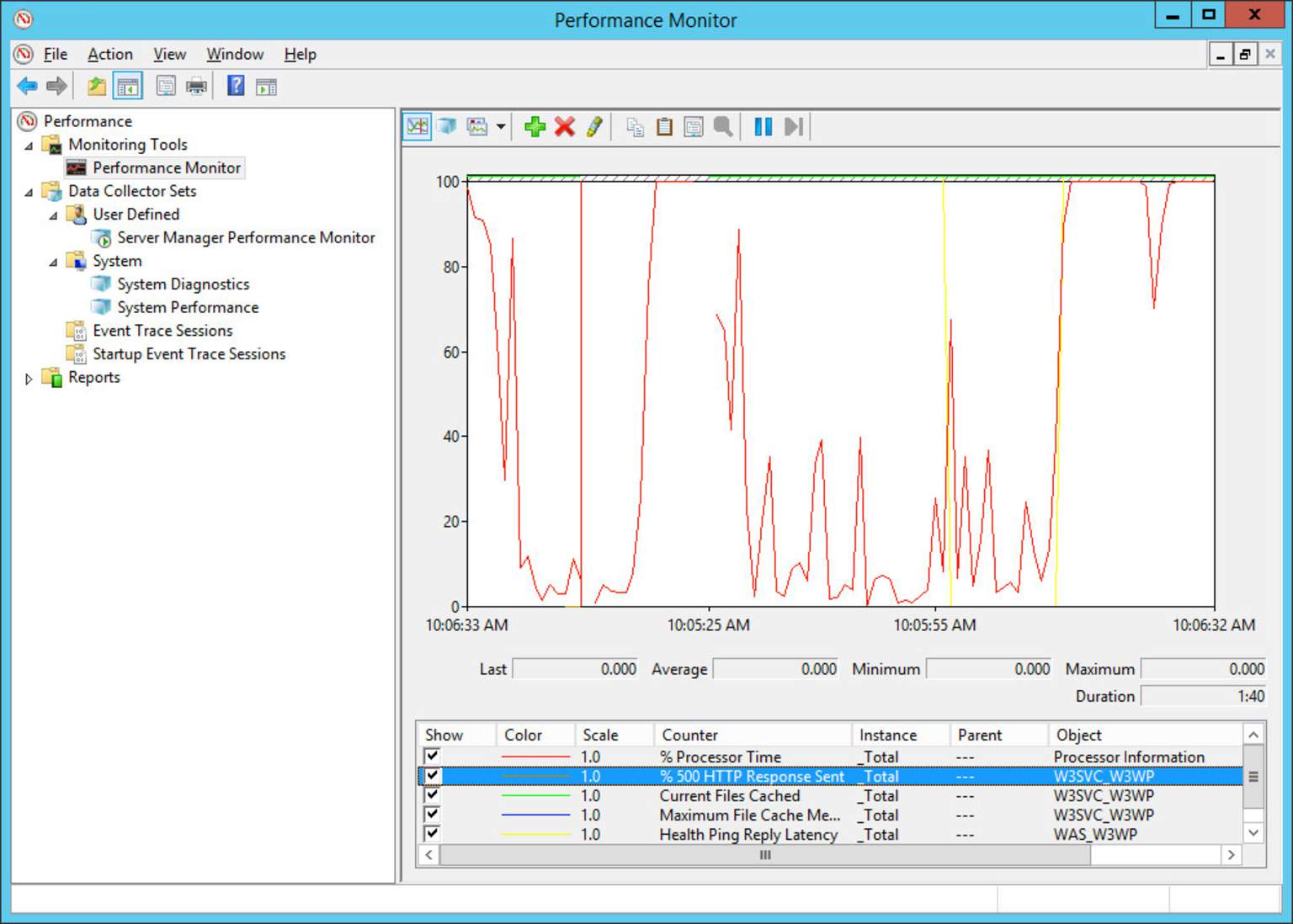
- Your ASP website encounters too many HTTP 500 errors "Internal Server Error"
- Your ASP website encounters frequent HTTP 503 errors "Service Unavailable" or "Server Too Busy"
- You need to improve IIS Application Pools recycling
- The security of your application does not meet your expectations
We know how to deal with the following layers of your infrastructure:



















Our IIS server audit and diagnostics methodology
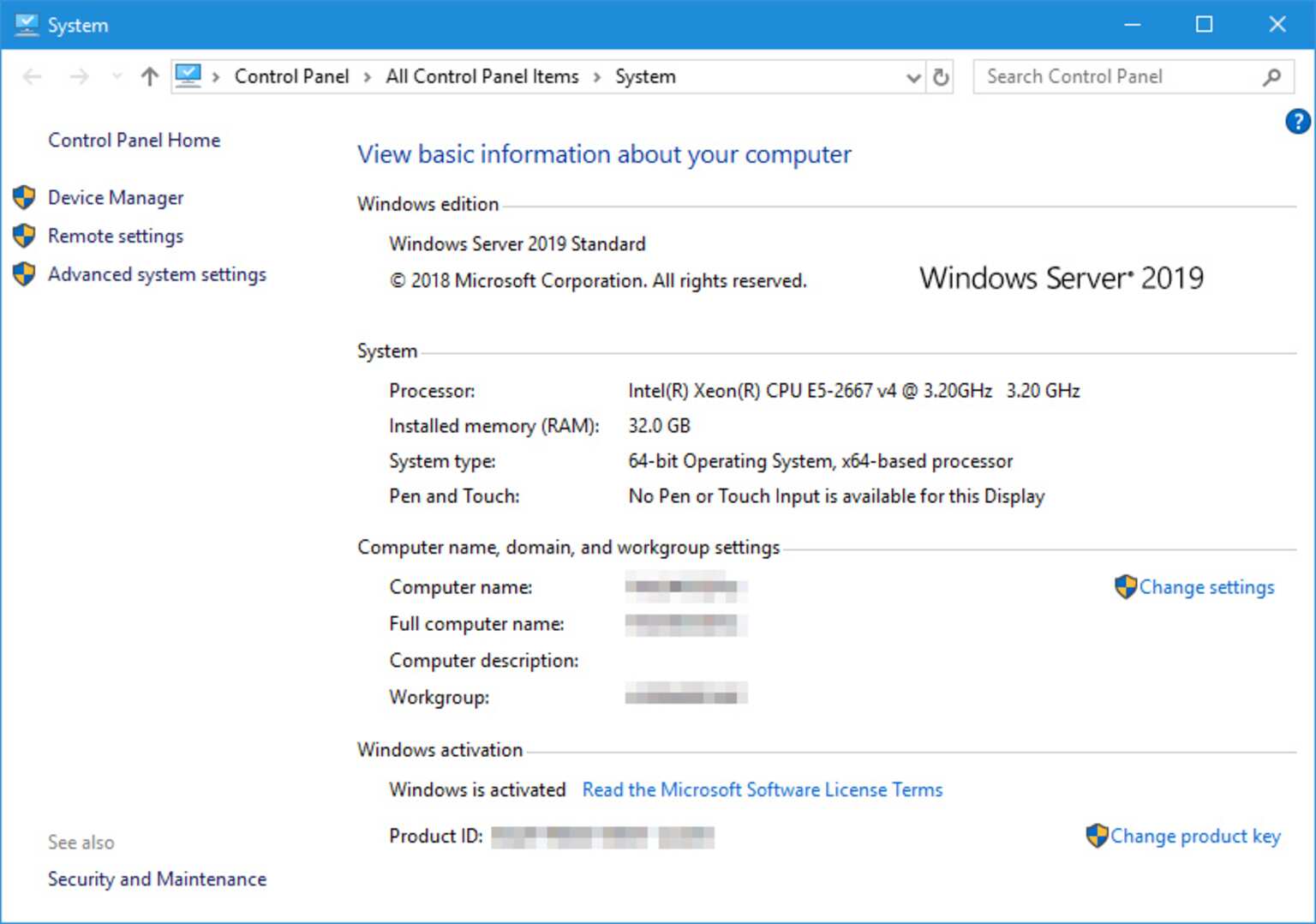
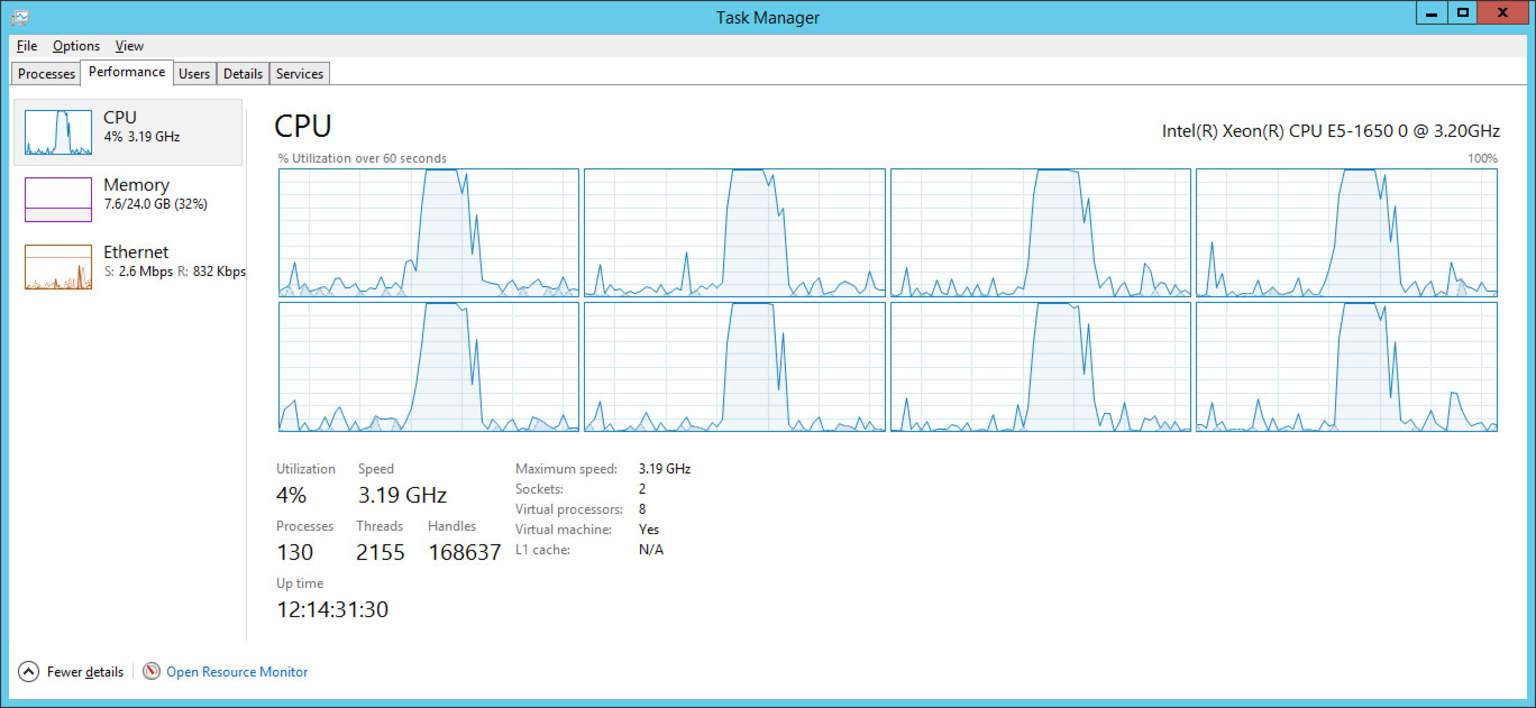
We have configured many Microsoft IIS 7/8/10 servers over Windows Server 2000 to 2025 systems, although we now recommend our customers to migrate to Windows Server 2019 or 2022 as a minimum. Our Auditing and Diagnostics methodology aims to identify the symptoms that affect or alter the operation of your Classic ASP application (ASP 3); we break our analysis into several phases:
Description of the concerned infrastructure:
We precisely identify the type of hardware (or virtual) server, and software that you are asking us to audit.
Description of the encountered symptoms:
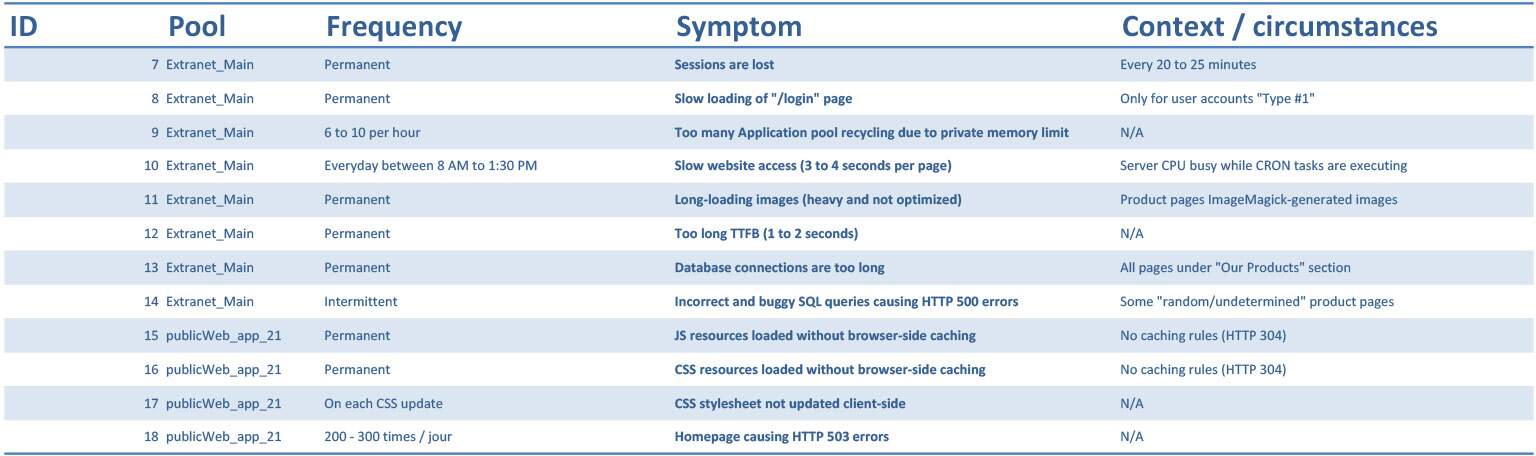
We establish a precise and exhaustive list of the technical symptoms that you encounter and for which you wish us to make recommendations.
Audit and detailed diagnosis of IIS:
- Review the general configuration of your Windows server,
- Review of the general IIS Web server configuration,
- Examination of the specific concerned website configuration,
- Examination of the IIS Application Pool(s) running your ASP code, including parameters affecting the sessions management and duration, queue limits management, memory management, temporary files parameters, Application pool(s) recycling conditions, Handlers order, compression parameters, cache rules, URL rewriting parameters,
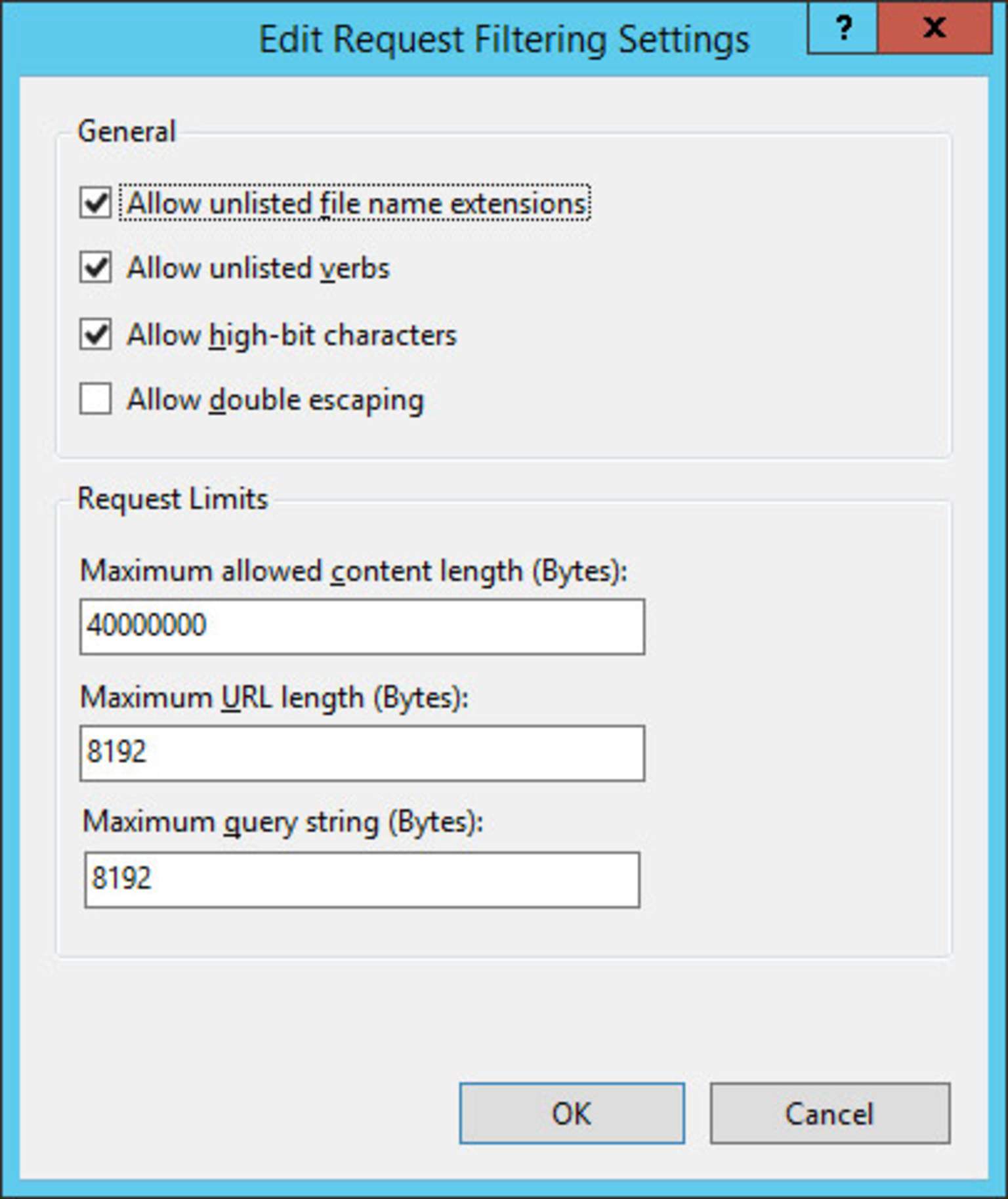
- Examination of the System.WebServer configuration, including properties referring to requests limits, HTTP responses, session-related properties, concurrent connections and scripts execution timeout parameters,
- Review of the HTTP web server registry keys and values.
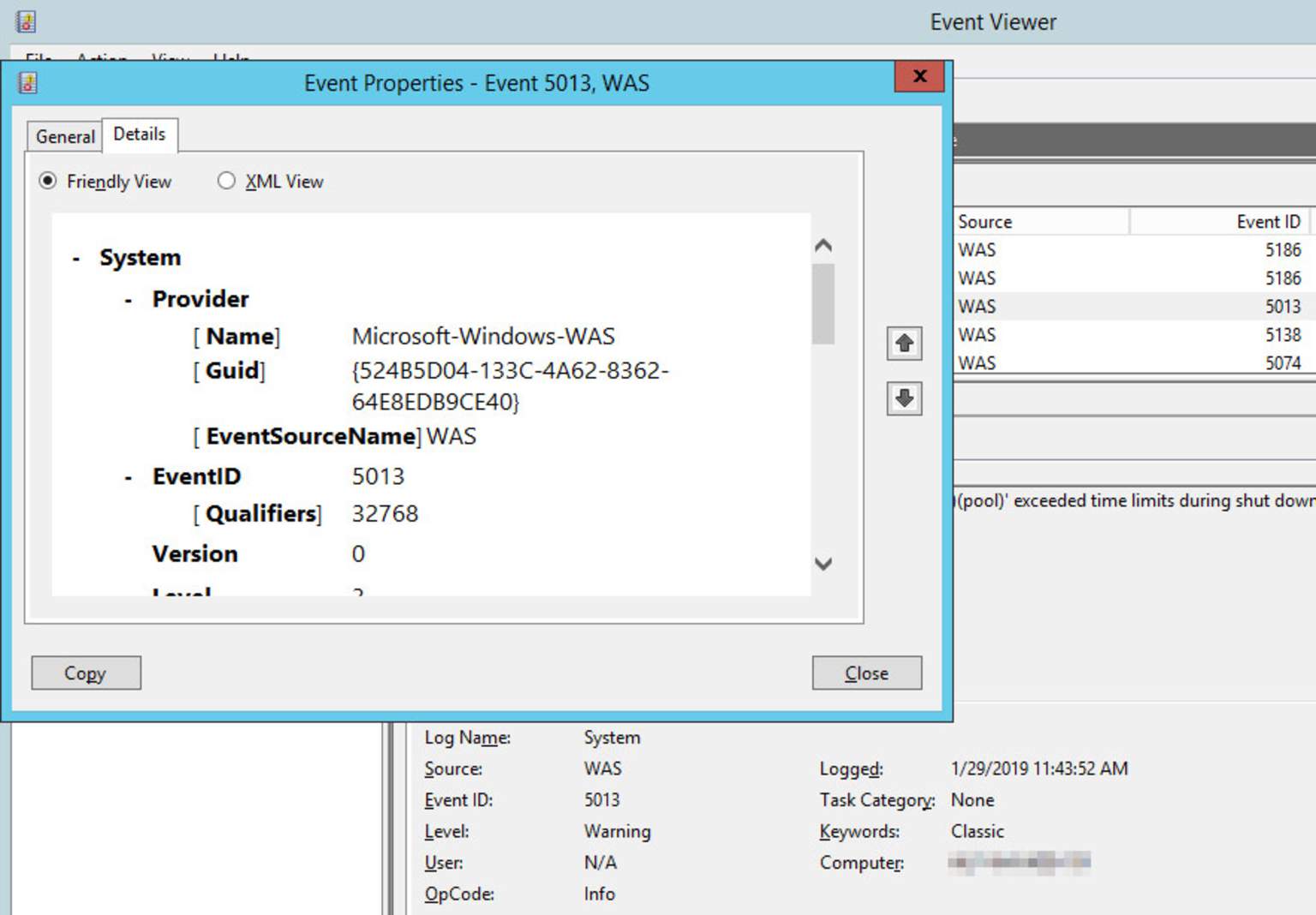
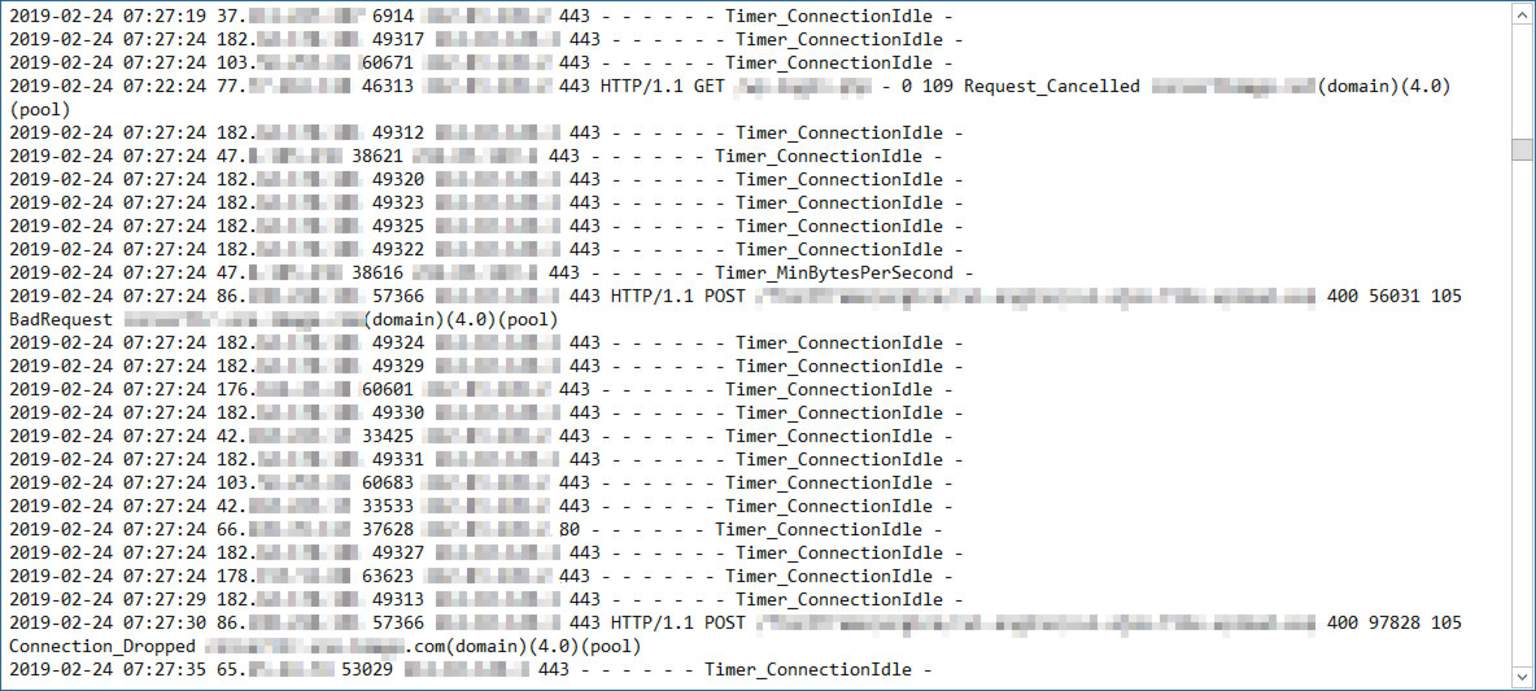
Analysis of the Windows Events, IIS & HTTP logs:
We carefully vet and review the log files generated by IIS (IISW3C), the HTTP service (HTTPERR), and also the IIS Application pools related events that were collected into the Windows Event Log.
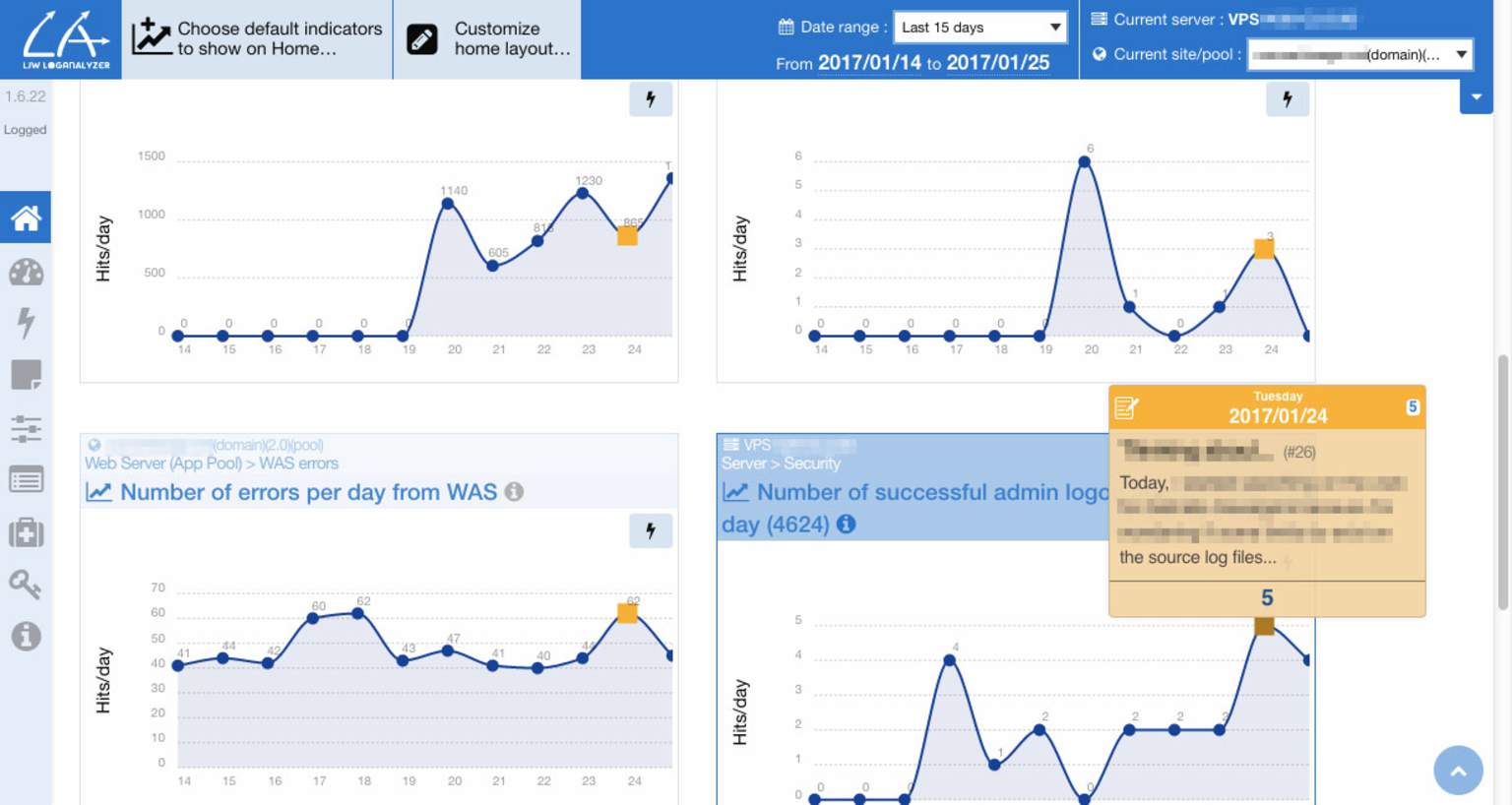
Our team have engineered and developed LJW LogAnalyzer®, our own logs collection & analysis application for improving the Microsoft IIS performance, which is based on Microsoft Logparser 2.2 on which we have great expertise.
LJW LogAnalyzer® is live and running on many production servers at our customers, who use it to proactively monitor the state of their system, to detect the source of bugs and errors in their ASP scripts.
Detailed analysis report:
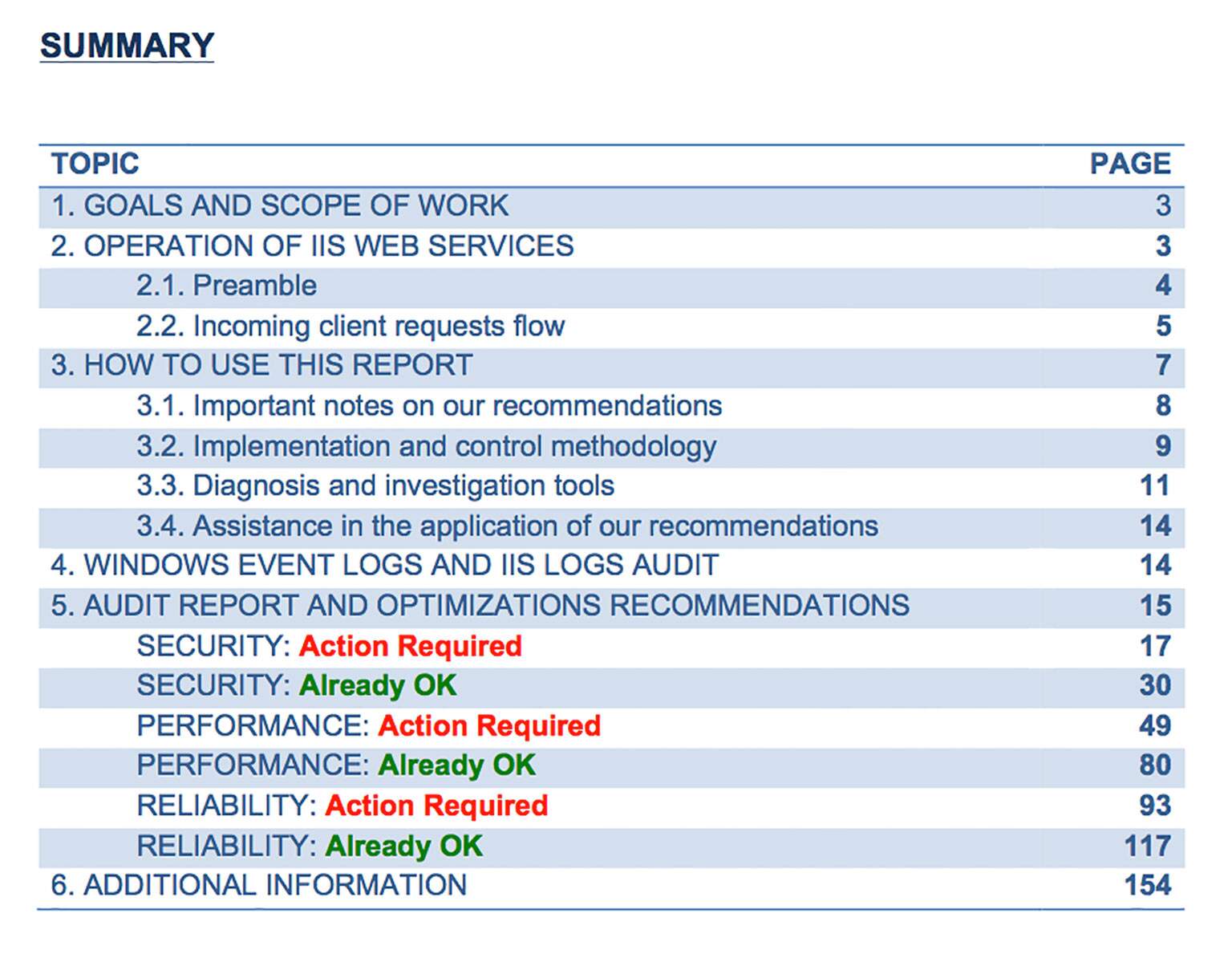
We provide you with a comprehensive report containing all verified points, black spots and bottlenecks discovered, instances of memory overuse and / or hard drive resources, and other topics to prospect on your side.
This document include a detailed and prioritized list of recommendations and optimizations, including tips on how to set them up, and information on the expected improvements and positive impacts. More than 180 individuals IIS settings are carefully checked. Our audit report contains 120-150 pages of very valuable clear and comprehensive information and tips on each parameter, including the way it needs to be configured on YOUR system. And we can apply them for you.
We provide you with details of all the actions carried out. This allows you to reduce your dependence on us, and allows you to capitalize on the knowledge we transfer to you. It is thus easy for you to learn, train, apply by yourself, and ensure the sustainability of your system.
Changes Scheduling
Debriefing and meetings by phone and / or Google Meet or MS Teams, ranging from 1 to 8 hours divided into several sessions, to develop the action plan to be implemented.
IIS Configuration tuning
Application of corrective actions by us, or in support of your internal/external IT teams. Following the debriefing with your teams, we will be able to apply or assist your teams on the points we will define together.
Post-action Control and tracking
We control the applied changes and observe the performance gains, as well as tracking the eventual side effects.
Limits of our IIS configuration audit service
Although we have a recognized expertise in detecting causes of malfunctions affecting the operation of Microsoft IIS, we obviously cannot guarantee you an absolutely certain "miracle" solution about the cause of your symptoms, because of the specificity of each system.
There are many good practices we know, which are essential to improve and fine-tune the configuration of an IIS server for the sake of ASP scripts, but there is no official checklist of a foolproof set of adjustments to be applied to obtain a "zero errors" operation.
The purpose of our audit & diagnostic analysis is to provide you, as a deliverable, with a detailed report including a list of recommendations and optimizations that can be: possible, mandatory, recommended, and / or critical.
Please note we have a wider leeway for action when working on dedicated hosting. Shared hosting is sometimes subject to many limits imposed by your hosting company, which prevent us from adjusting all the parameters that might be required in certain situations. However, we are able to bring many optimizations to your source code. Our shared hosting offers are specifically designed for ASP 3.
Once implemented by your IT teams and / or with our support, these recommendations will be able to overcome or regulate all or part of your symptoms, make your infrastructure more stable, and reduce the number of daily encountered errors, thus improving your ASP application quality.
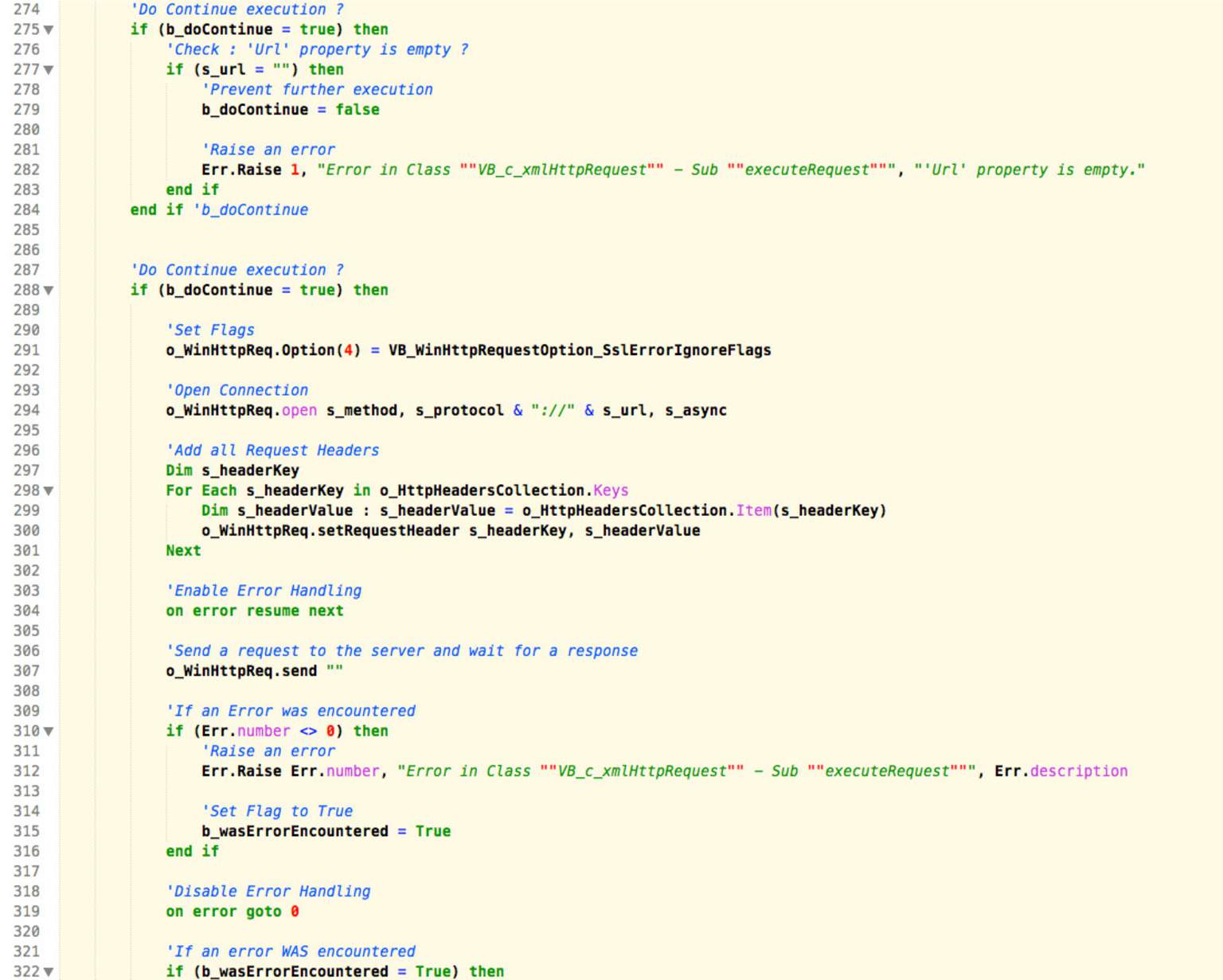
We draw your attention to the fact that a significant part of an ASP Classic application performance directly depends on its source code, and how it uses and consumes ActiveX/COM+ components.
We are qualified to audit your ASP source code and apply optimizations to it that will allow you substantial performance gains. Please get in touch with our team if you need to improve the quality of your ASP Classic scripts and streamline their structuring.
We tune your IIS configuration methodically
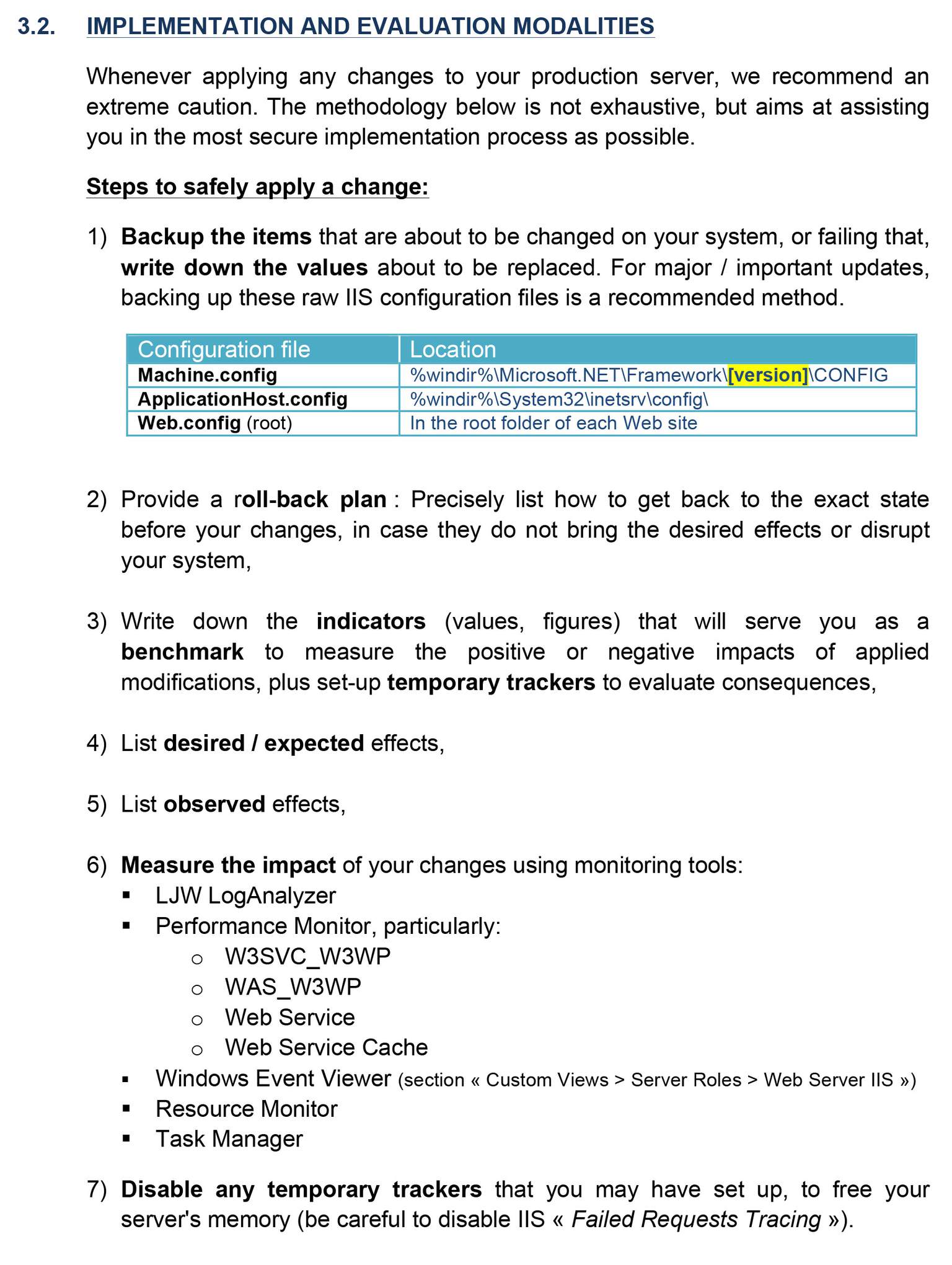
We know that going "rummage" through the arcanes of the "Configuration Editor" and the "applicationHost.config" files is a delicate operation that need to be performed with calm, method and precaution. For this reason, each of the optimizations we make is based on a specific argument coming from the report we give you following the audit of your actual configuration. We then apply changes in a structured way and in a prioritized manner.
We provide a rollback plan
Although our experience makes us sure of our recommendations, we know that no change is magic, and that edge cases can always occur. That's why we work with your IT teams to prioritize our recommendations and establish a secure deployment schedule so that the consequences of each change can be tracked and evaluated before continuing to apply further optimizations. In addition, to provide optional rollbacks abilities, all applied tuning and their implementation date are recorded, as well as the effects and consequences noted as output. This way, nothing is definitive or irreversible.
A preserved integration of your COM+ components
While applying optimizations to your IIS server, we ensure that every integration of your ASP Classic code with ASP/COM+ components remains fully functional. We are also qualified to improve the usage your source code makes of these components, including decreasing their memory impact on your server, or their CPU time, which will result in faster ASP scripts. Contact our team to lighten the load of these COM + components on your ASP scripts.
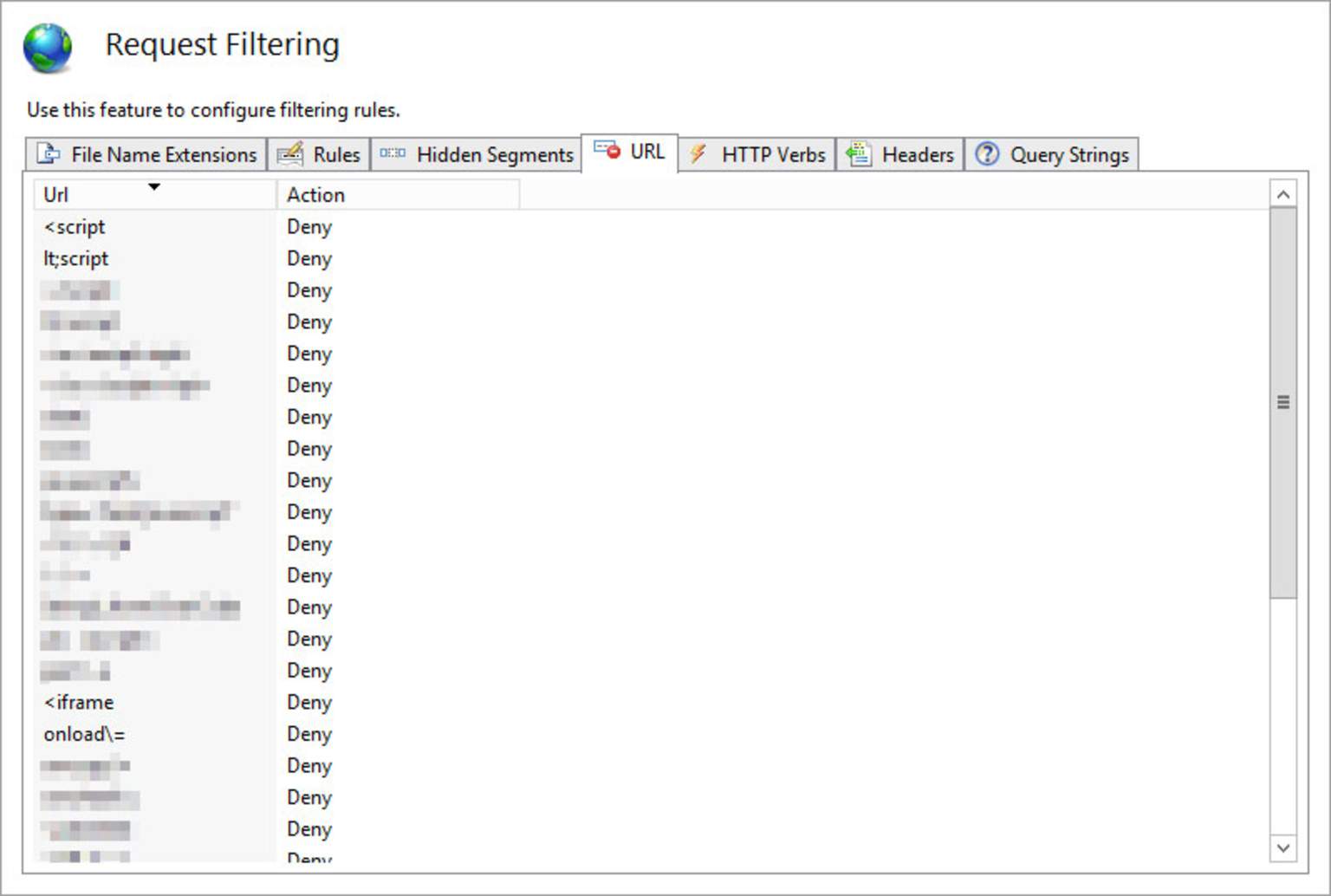
Advanced "web.config" rules
Our many years working on Microsoft Internet Information Services gave us the knowledge of which parameters to act on in order to increase the reliability of your ASP 3 applications. We thus control the rules of your "web.config" file, the parameters of the "applicationHost.config" file, as well as their hierarchical inheritance chain. We can step in at your "web.config" files level in order to secure accesses and URL sequences, or setup efficient rewrite and redirection rules (rewrite 301) having a strong beneficial impact on your website SEO.
Conversion of HeliconTech ISAPI_Rewrite rules
We can also convert your old rewrite rules based on HeliconTech ISAPI_Rewrite 3 to native IIS "web.config" files. HeliconTech ISAPI_Rewrite 3 was a very popular product back in the IIS 6 and IIS 7 days. It is an ISAPI filter offering functionality for creating rewrite rules within .htaccess files similar to Apache's mod_rewrite module. Migrating these rewrite rules to IIS native "web.config" files brings you performance gains, improves the maintainability and sustainability of your code, and frees your Classic ASP app from this ISAPI filtering layer.
Windows Server installation and configuration
& migration to Windows Server 2019/2022/2025
If you are installing Windows Server, we are at your side to configure it the way it will benefit from maximized performance, particularly at the IIS web server level. We configure several parameters at the Windows level too, such as the ones found under the "Local Group Policy Editor" and "Local Security Policy".
We also regularly support many clients in their migration to Windows Server 2019 / 2022 / 2025. Our experience guarantees you that we tune the IIS web server parameters appropriately to ensure that your ASP sites run flawlessly. Discover our service.

We respect an absolute privacy
We know that giving us an access to your production servers is one of the most important decisions. Your critical applications must not suffer from any approximation, nor never be at risk. That is why, as part of each of our IIS server audit engagements, we redact a written document in which we explicitly commit ourselves to many points. This document is aimed at clarify our intervention perimeter with your IT department and your legal department.
More details are available in our Conditions and Terms of Use.
- During the audit and diagnostic phase, we will not make any changes to your system, configuration, data, or source code. As a result, no malfunction can be attributed to us during this analysis phase, and your application will continue to operate in its initial state.
- We are committed to maintaining strict a confidentiality and an absolute security regarding all information to which we will have access, including: your source code, your infrastructure and the software you operate, the configuration of your system, your business data, access codes that you will communicate to us.
- We respect a full transparency towards you regarding the requested service providers. We prohibit ourselves from subcontracting any portion of our services to a third party, except in the case of an explicit agreement with you, specifically mentioning the concerned parts of the work.
- Being fully aware of the criticality of your infrastructure and data for your business, we officially commit ourselves to :
- Only download the files we need, and do not keep any copies after, —according to your choice—, the date of delivery of our recommendations, or the closing date of our corrective action application,
- Allow access to your server to only one member of our team, whose a copy of the ID Card will be communicated to you, and to only work in normal fatigue and lucidity conditions, by banishing the use of any psychoactive substance of any type,
- Only store any downloaded data and access codes on a single workstation in our own office, running a "Non-Windows" operating system (Linux or MacOS), password-protected, accessible to the sole member of our team in charge of auditing your server, secured with licensed and up-to-date Antivirus software plus a bi-directional firewall regularly updated and configured in "Paranoid" mode. We guarantee you that no external access to this workstation is possible,
- Access your data, servers and tools only from a private internet access whose characteristics and IP address will be communicated to you before the beginning of our audit mission,
- Never access, under any circumstances, your data, servers and tools from another unsecured connection (public WIFI, HotSpot, ...) than the above-mentioned connection on the previous point,
- Under no circumstances assign or disclose, with or without charge or compensation, all or part of the data, access codes, specific features or configurations of your system to any third party, whatever the current or future circumstances,
- Never use, for a permanent and unlimited duration, all or part of the source code of your application for one of our current or future developments, for our own services or one of our other customers, whether in our current legal form, or any other legal form that we may adopt in the future.
- As a result, the only benefits that we allow ourselves to draw from this work for you, are:
- The perception of the financial emoluments agreed in our estimates/quotes,
- An improvement of our technical knowledge, of which nothing will never allow to identify your entity.